A cybersecurity firm took 48 Gbps mid-training. Flowtriq stopped it before 240 students noticed.
Multi-vector 48 Gbps attack against a live Lorikeet Security public training event stopped by Flowtriq's per-second detection and unified BGP FlowSpec and cloud scrubbing upstream mitigation, with zero impact to 240 attending participants.
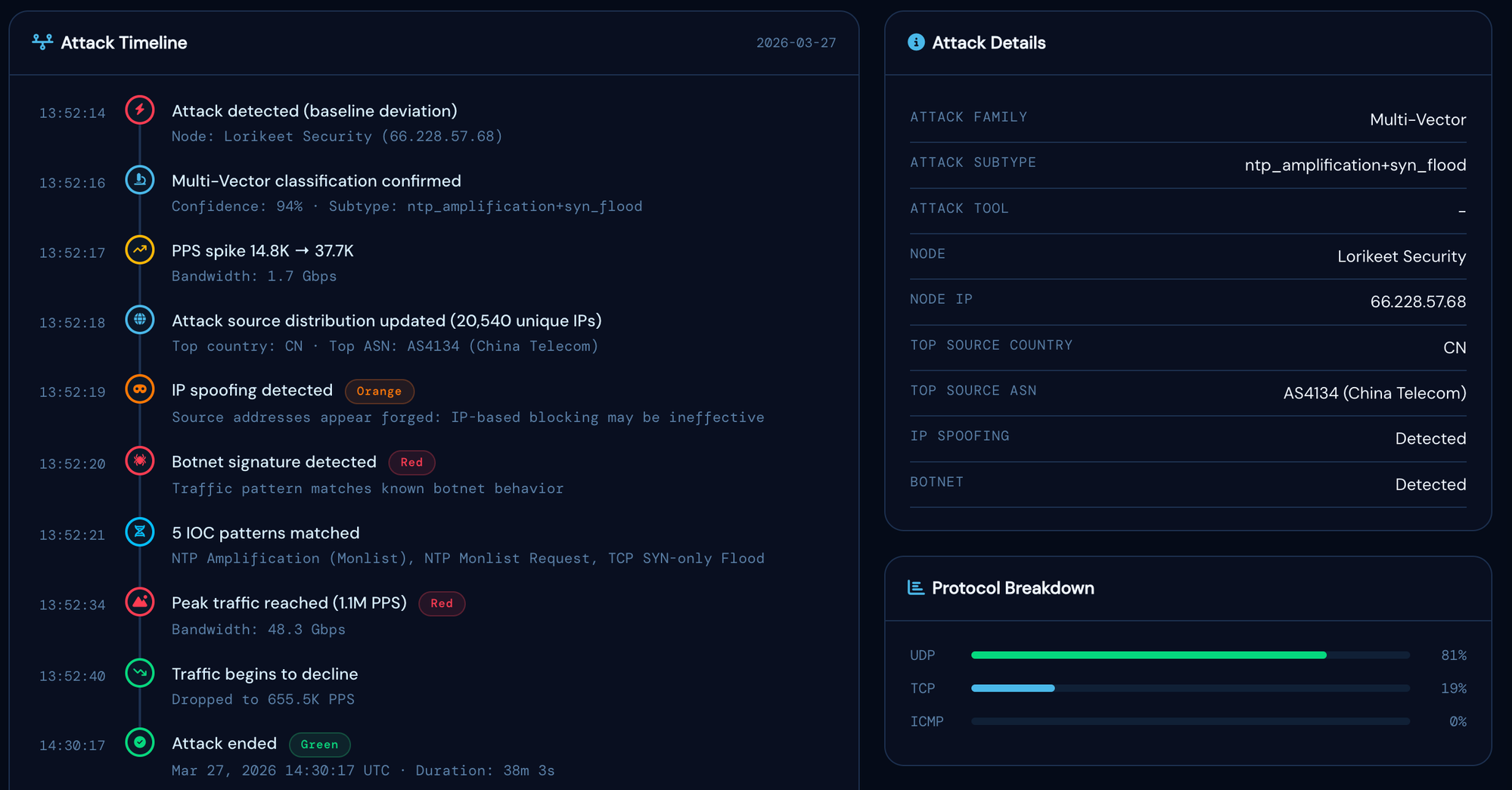
Flowtriq, a real-time DDoS detection and mitigation platform, and Lorikeet Security, a cybersecurity training and threat simulation firm, today announced the results of Flowtriq's deployment across Lorikeet's live cyber range infrastructure. During a March 27, 2026 public live cybersecurity training event attended by 240 participants, Flowtriq detected a multi-vector DDoS attack within 0.9 seconds of the first malicious packet, automatically applied on-node mitigation rules, and pushed BGP FlowSpec drop rules to Lorikeet's upstream transit provider within 11 seconds via unified BGP FlowSpec and cloud scrubbing upstream mitigation, with the training session continuing uninterrupted throughout.
The attack, a coordinated multi-vector campaign combining NTP amplification (peaking at 39 Gbps and 1.06 million packets per second) with a spoofed SYN flood (890,000 SYN/s across 18,400 source IPs), targeted the training platform and CTF challenge server simultaneously. Conventional monitoring approaches would have required manual identification of the attack, determination of mitigation strategy, and manual coordination with the upstream provider, a process typically measured in minutes rather than seconds. Flowtriq completed the full detection-to-upstream-mitigation cycle automatically in under 12 seconds.
"We had 240 people in a live cybersecurity event and took close to 50 gigabits of attack traffic mid-session. The Flowtriq alert landed in our Slack before I'd even registered anything was wrong on the dashboard. On-node rules fired, BGP FlowSpec pushed upstream, cloud scrubbing active. Full mitigation stack in under 15 seconds from detection. Not one participant noticed."
Lorikeet Security operates a live hands-on training events program delivering instructor-led adversarial network exercises to enterprise security teams, government contractors, and university programs. Events are delivered against dedicated bare-metal infrastructure and carry a hard uptime requirement: any degradation during a live session directly impacts the training experience and Lorikeet's operational credibility. The March 27, 2026 event ran for a full day across three nodes (training platform, CTF challenge server, and media relay), all of which remained fully operational throughout the 38-minute attack.
"The Lorikeet event is exactly the scenario Flowtriq is built for: a hard deadline, a public-facing IP, and no tolerance for downtime. The fact that the infrastructure team was able to handle a near-50-gigabit multi-vector attack through a single interface (alert in Slack, mitigation rules pushed upstream, session continuing) and their participants never noticed anything happened, is what per-second detection and integrated BGP mitigation actually delivers in practice."
Following the March 27 event, Lorikeet Security has standardised Flowtriq across all event infrastructure as a required component of pre-flight. Every session now includes a dedicated check: FlowSpec adapter connected, cloud scrubbing integrations verified, alert channels confirmed. Flowtriq runs year-round on all three nodes.
About the Attack
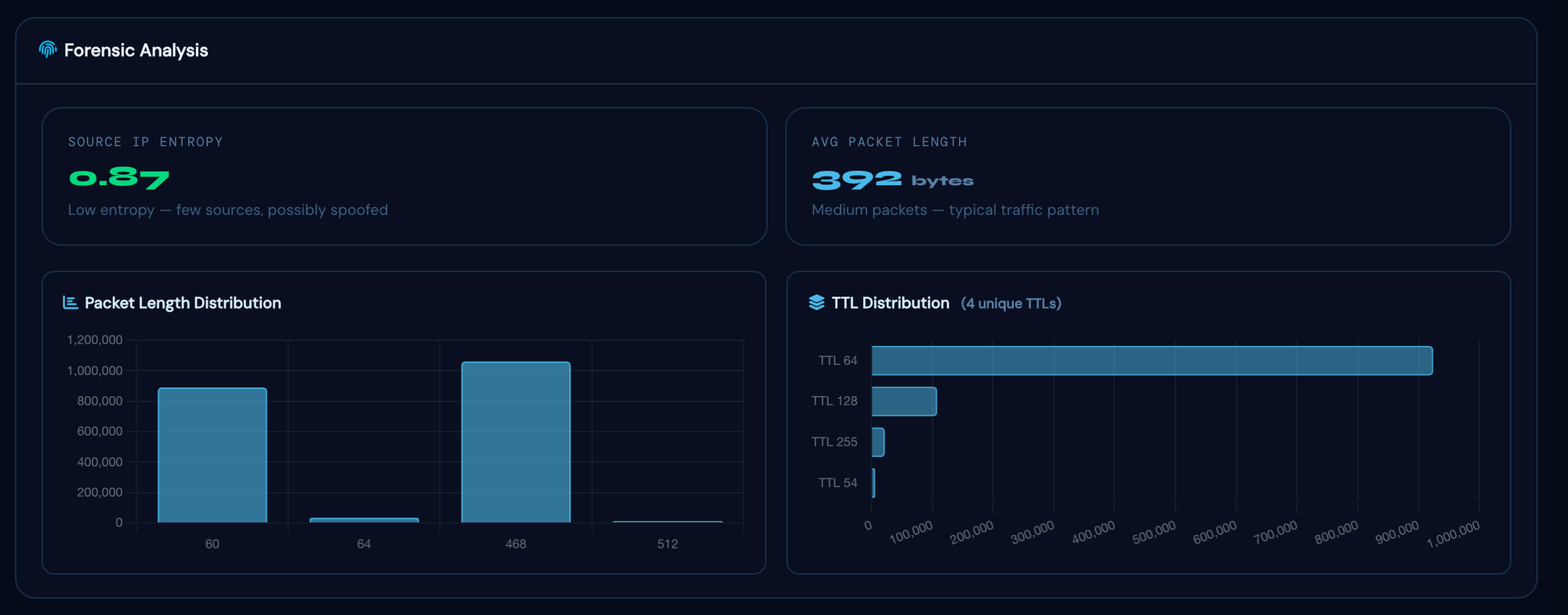
Post-incident analysis of the Flowtriq-captured PCAP confirmed the attack originated from two distinct botnet campaigns: a large-scale NTP amplification reflection leveraging approximately 2,140 open NTP reflectors primarily located in China, the United States, South Korea, Russia, and Brazil; and a spoofed SYN flood targeting TCP ports 443 and 8443 from approximately 18,400 source IPs. The two-vector structure was identified by Flowtriq as a single multi-vector incident within the initial 0.9-second detection cycle, enabling targeted FlowSpec rules for each vector rather than a broad blackhole response.
Availability
Flowtriq is available now at flowtriq.com. Plans start at $9.99/node/month with a 14-day free trial and no credit card required. BGP FlowSpec and RTBH upstream mitigation adapters are included on all plans and support ExaBGP, GoBGP, BIRD 2, FRRouting, and major transit providers. A full case study detailing the Lorikeet Security deployment is available at flowtriq.com/blog/lorikeet-security-case-study.
About Flowtriq
Flowtriq is a real-time DDoS detection and mitigation platform for infrastructure operators. The Flowtriq agent installs in under two minutes on any Linux server, learns the node's baseline traffic in approximately five minutes, and detects volumetric and protocol attacks in under two seconds. Integrated BGP FlowSpec, RTBH, and cloud scrubbing adapters enable automatic or one-click upstream mitigation. Flowtriq is used by hosting providers, game server operators, managed security providers, financial services firms, and individual infrastructure operators globally. Flowtriq is a product of Traztech Inc., headquartered in Toronto, Ontario, Canada.
Website: flowtriq.com
About Lorikeet Security
Lorikeet Security is an Orlando, Florida-based cybersecurity firm offering penetration testing, red team operations, and compliance consulting. Through their Lorikeet Security training events platform (formerly Parrot CTFs), Lorikeet hosts live CTF competitions and hands-on cyber training events for enterprise security teams, government contractors, and academic institutions. Founded in 2021 by Ryan Wilke, Lorikeet has hosted 50+ events with over 15,000 participants trained to date.
Website: lorikeetsecurity.com
Media Contacts
Flowtriq
Jacob Masse, Founder
Toronto, Ontario, Canada
[email protected]
Lorikeet Security
Ryan Wilke, CEO & Founder
Orlando, Florida
[email protected]
Media Assets
High-resolution headshots, Flowtriq dashboard screenshots from the March 27 incident, event photography, and logo files (SVG/PNG) are available on request. Contact [email protected].

